How to Align Workforces for AI Adoption Without Triggering Shadow-AI
Shadow-AI grows when sanctioned channels are harder than personal workarounds. Six tactics for matching ease-of-use while keeping governance intact.
Avoid California’s Misclassification Trap: How to Hire Fractional Executives
California's 2025 Iloff ruling ended the good-faith defense for misclassified workers. Here are three paths founders can take to hire fractional executives safely.
Calling the Agency Bluff: How California’s AB 692 Killed the "No-Hire" Penalty
California's AB 692 voids the "stay-or-pay" clauses agencies use to lock in engineers. Here's why their six-figure demand letters are running on dated case law.
The Founder’s Guide to Agency Contracts: Red Flags, California Law, and Avoiding Vendor Lock-in
Agency contracts often hide IP traps and no-hire penalties designed to lock founders in. Here's how to spot the red flags and push back.
The AI Arbitrage Trap: Why Startup Founders Are Abandoning Hourly Agencies
AI cuts development time 30-45%, but hourly agencies pad estimates to capture the margin. Founders are shifting budgets to fractional partners with fixed scope.
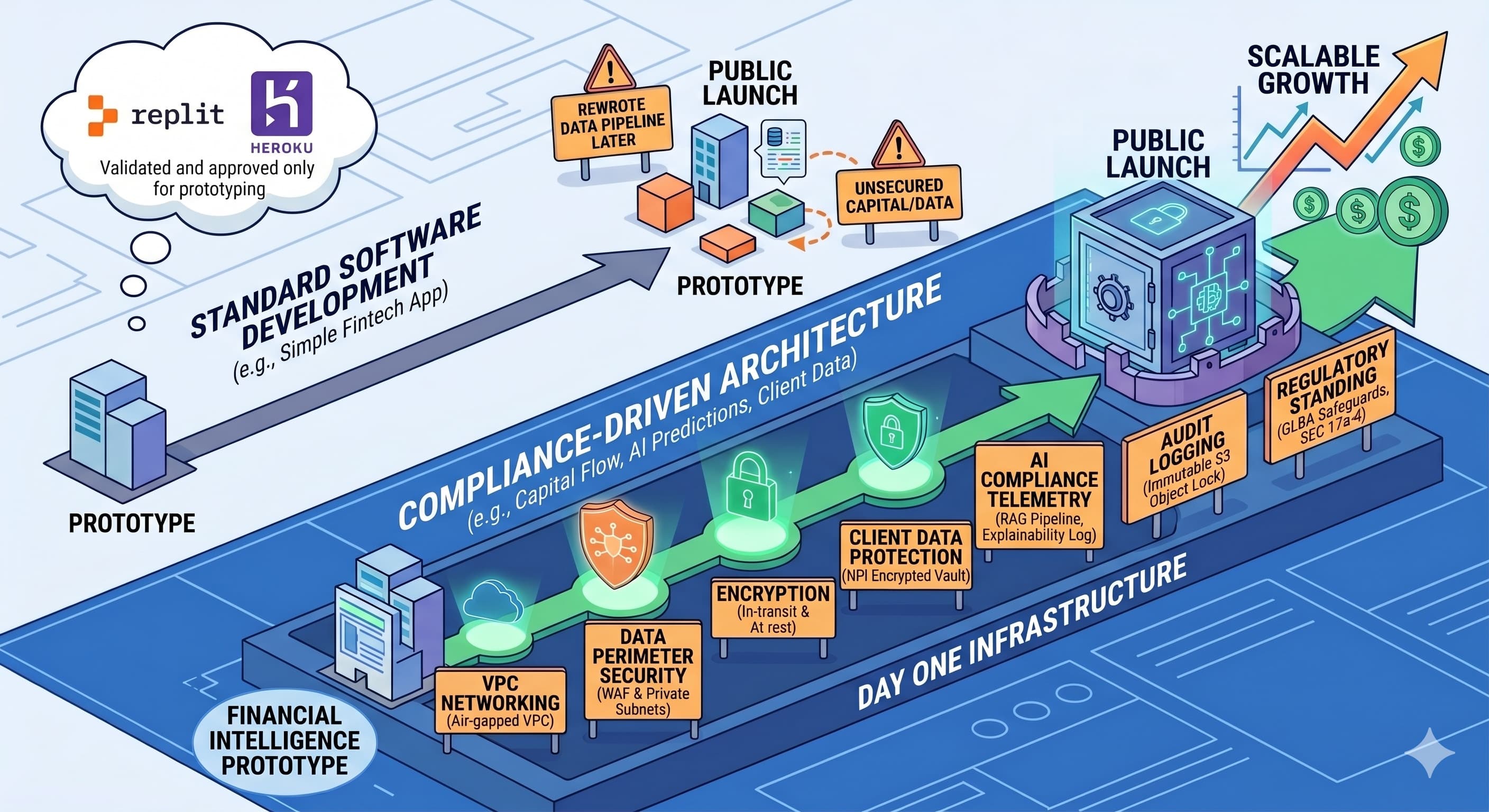
Crossing the Line: When a Startup MVP Triggers Cloud Compliance
Adding user profiles or sensitive features to an MVP can trigger HIPAA, GLBA, FERPA, or COPPA oversight, reshaping cloud architecture requirements before launch.
Read moreAEO Pugmill: A 3-Prong Startup
A three part startup that provides advanced AI-native publishing features, answer engine optimization, and builds a unique dataset.
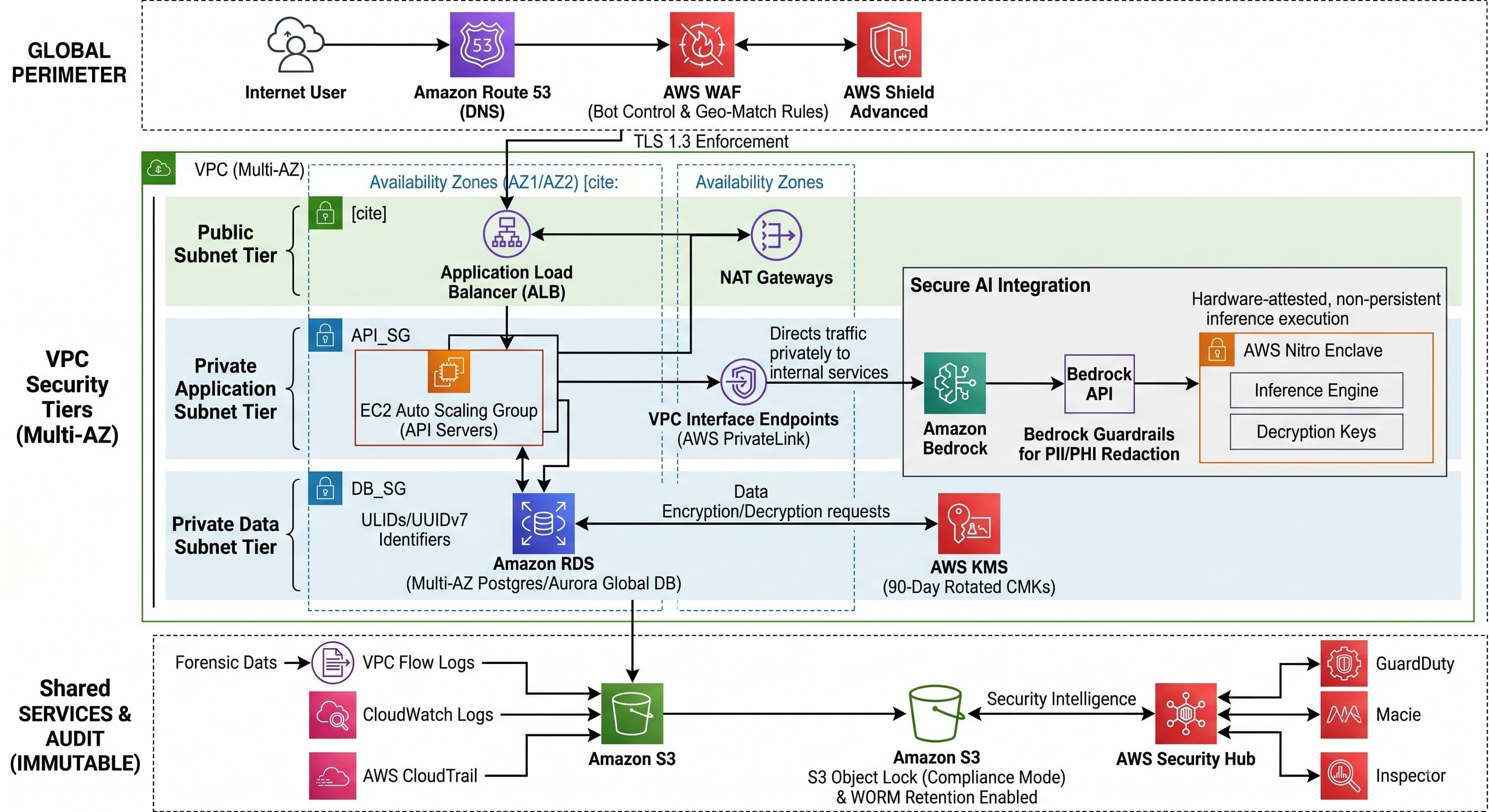
Developers' Guide: Configuring AWS Infrastructure for Regulated Data Workloads
Mapping HIPAA and GLBA requirements to AWS services, from WAF perimeters and VPC segmentation to KMS rotation, Bedrock Guardrails, and S3 Object Lock audit trails.
Startup Founders' Guide: Guidelines for GLBA-Compliant AI Cloud Architecture in Financial Services
Building AI-driven FinTech requires GLBA-compliant architecture from day one. Here's how to structure cloud infrastructure that satisfies SEC oversight without rewriting later.
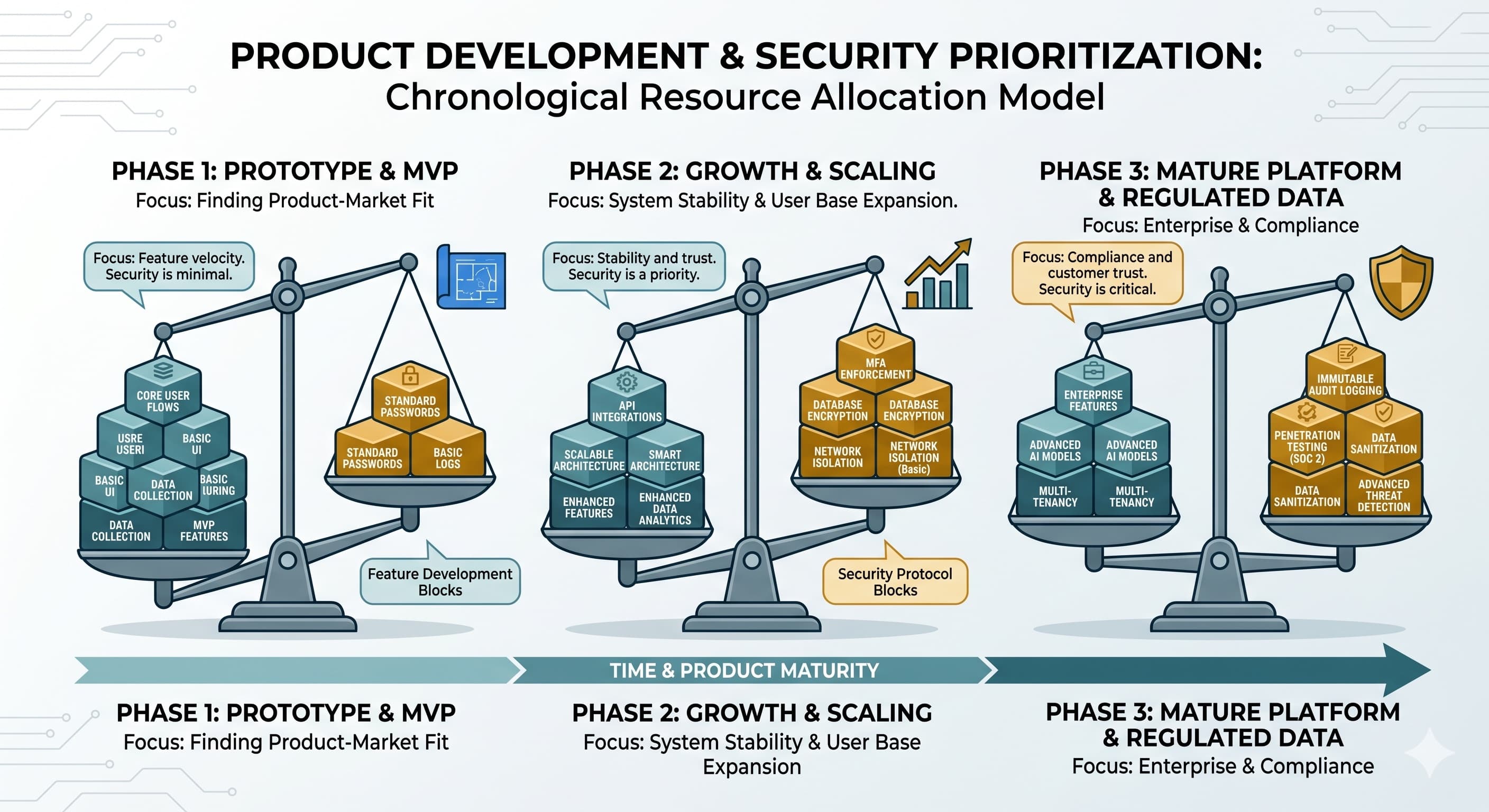
Balancing Product Development and Security Protocols
Allocating engineering hours between features and security depends on what data the system handles. Mapping defenses to project milestones aligns spending with actual threats.